PlonK Deconstructed 9: Round 4
Ben Bencik

Round 4
The fourth round has little going on. The prover must compute openings to evaluate already committed polynomials. But there is a neat trick to make this more effective.
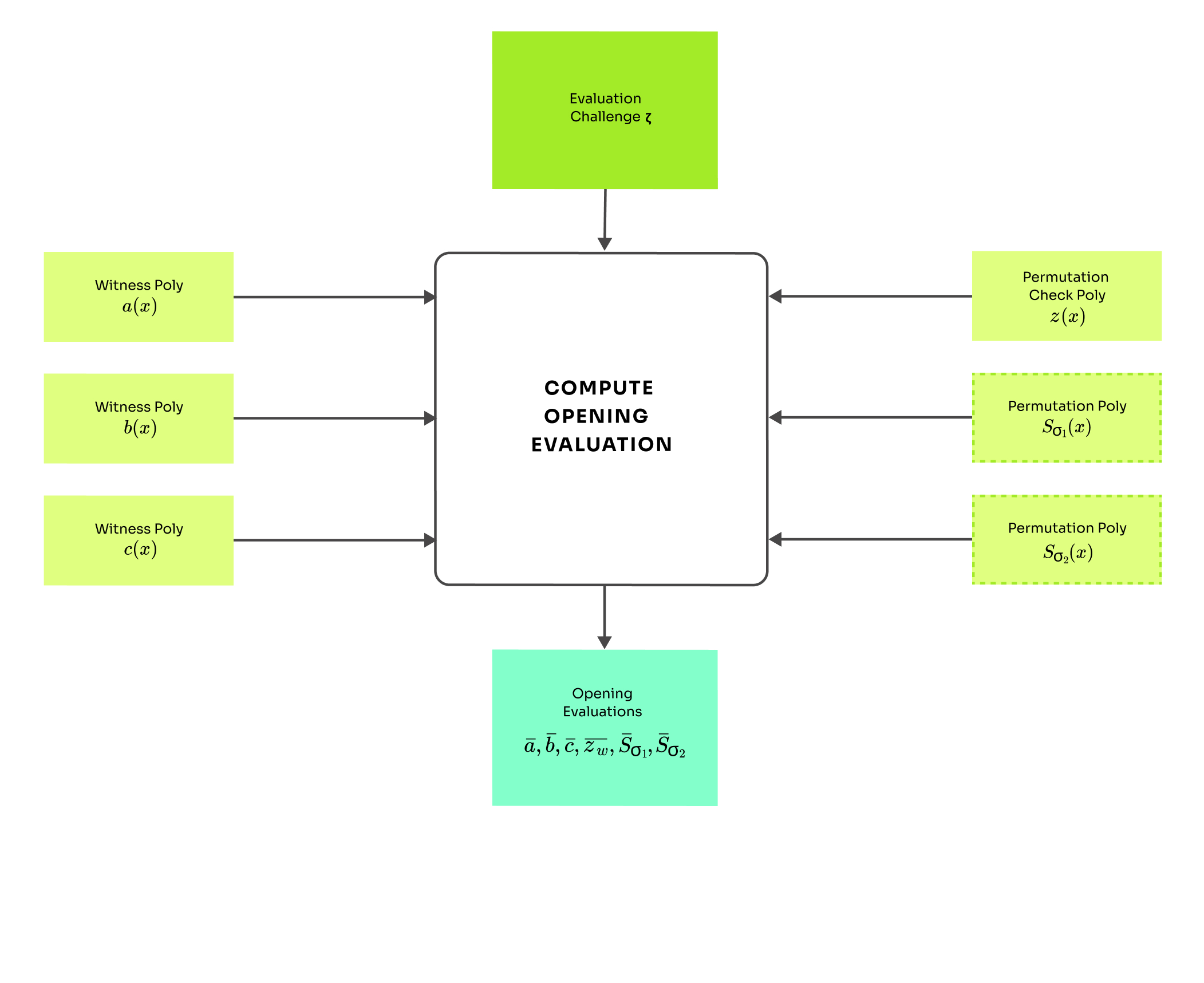
Round overview:
Compute evaluation challenge
Compute and output opening evaluations , ,
Linearization trick (Maller optimization)
Say that the prover wants to show that over the domain . We will denote terms with horizontal line as openings .
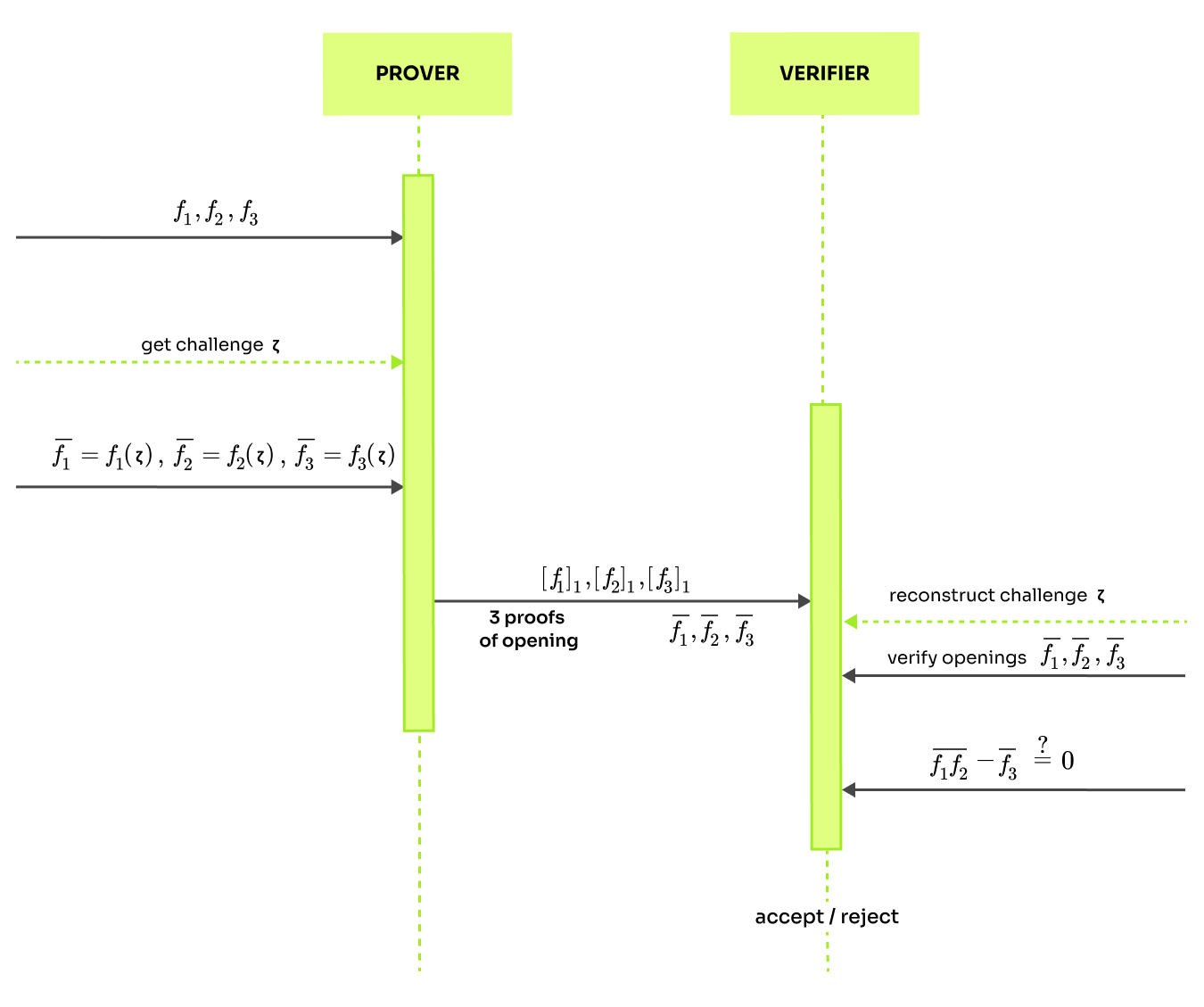
The standard way of proving this is to send 3 commitments and 3 polynomial openings at a randomly picked challenge and let the verifier check . Using the polynomial commitment scheme, the verifier can check if the openings are correct evaluations of the committed polynomials and as mentioned in math toolkit, it is sufficient to compare the polynomials at a single randomly picked point. In the interactive protocol, the verifier picks the challenge. In non-interactive case the challenge is picked by a random oracle after the prover commits to the polynomials.
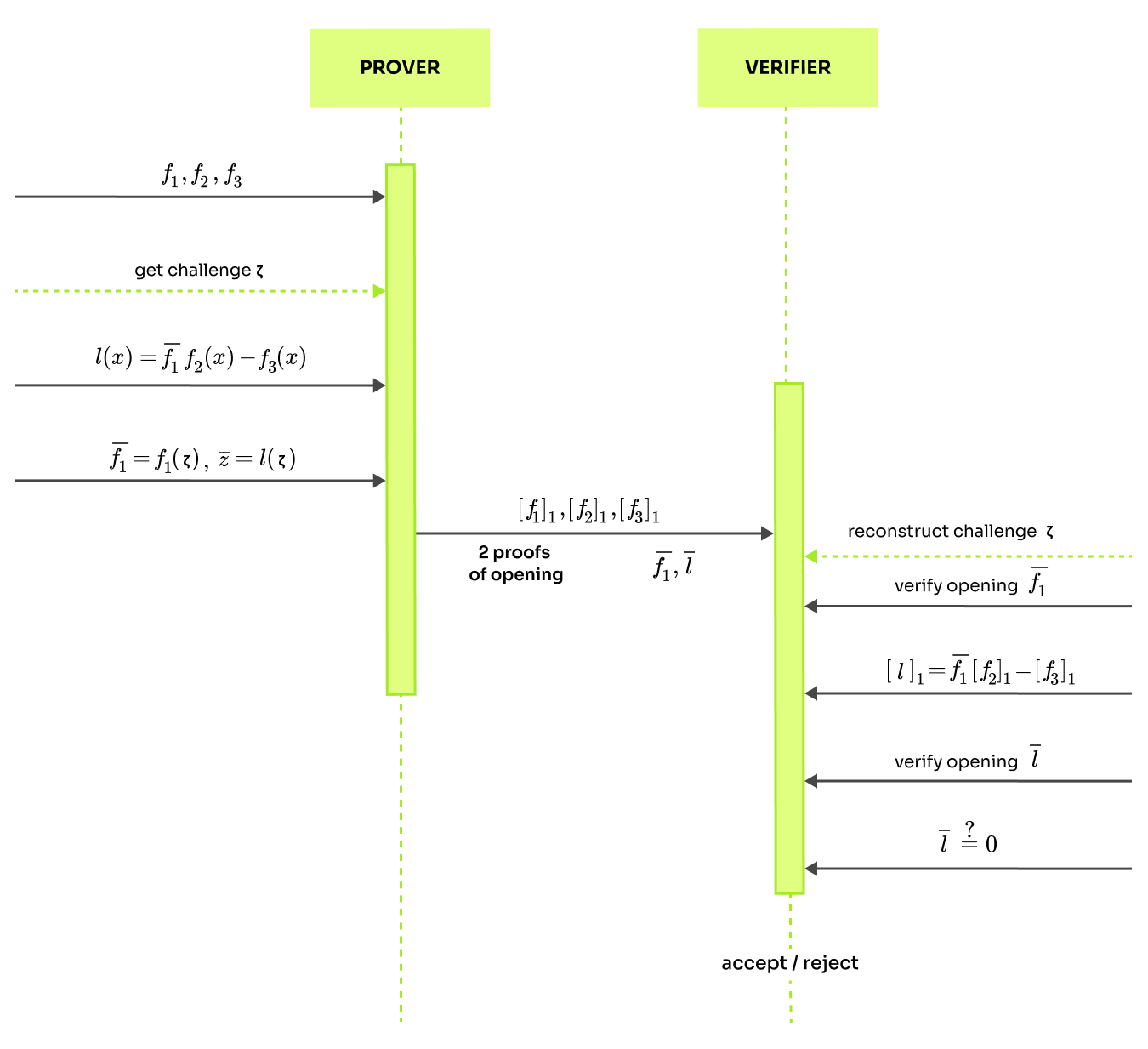
There is a better approach where the prover sends 3 commitments but just two 2 openings. This minimizes both the communication load and the proof size. The trick is in constructing a linearization polynomial: . As before the prover needs to send commitments , but only 2 openings and and two proofs of opening (from polynomial commitment scheme).
The prover does not send commitment linearization polynomial , because the verifier can calculate on his own. Revise commitments are defined as elements of a group defined by points on an elliptic curve over a finite field as explained in the KZG post. In the group, only one operation is defined between the group elements. This means that we can add commitments but not multiply them. However, it is possible to multiply a group element by a constant (in this case ) so we can calculate . This means that the linearization polynomial cannot contain polynomial multiplication, otherwise the verifier would not be able to calculate the commitment .
So, if the verifier can reconstruct commitment to the linearization polynomial , he is also able to check that the openings is a correct evaluation thanks to the 2 proof of opening he recieves from the prover. Since the linearization polynomial is constructed as it means checking is equivalent to checking . The whole linearization trick is described more formally on page 18 of the PlonK paper.
Polynomial openings
In this round, the prover does not construct any new polynomial and calculates just the opening at a challenge given by a random oracle. The non-interactive challenge generation is briefly explained in the round 1. The openings are calculated as: \bar{S},[object Object],2}
There are two things to notice about this. The prover sends evaluations but not and evaluation to the permutation polynomial is at instead of . If you would like to know why, continue to the final round of the PlonK prover algorithm.
List of the PlonK blog posts:
- 1: Overview
- 2: Arithmetization
- 3: Math Preliminaries
- 4: KZG
- 5: Setup
- 6: Round 1
- 7: Round 2
- 8: Round 3
- 9: Round 4
- 10: Round 5
- 11: Verification
If you have any suggestions or improvements to this blog, send an e-mail to contact@maya-zk.com


