PlonK Deconstructed 11: Verification
Ben Bencik

Verification algorithm
We have covered the whole prover algorithm in the previous posts. Now, we would like to show how to check the validity of the provided argument . Besides the common preprocessed input, there is also verifier preprocessed input consisting of commitments to public polynomials: . The polynomials are public, therefore the verifier can compute the commitments.
The first part of the verifier algorithm performs sanity checks on the commitments and openings, reconstructs the transcript to calculate the challenges, and evaluates some public polynomials.
Validate commitments
checks that the provided commitments are in the correct group. The group is constructed from an elliptic curve, so for each commitment, the elliptic curve equation must hold
Validate evaluations is even easier than the previous check. The verifier must ensure that each evaluation is in .
Validate public inputs check that the public inputs are elements of the field the same way as in the case above.
Compute challenges . In an interactive case, this is easy since the verifier is the one who generated the challenges. In non-interactive case, challenges are generated by a random oracle based on the transcript of the protocol as described previously. The verifier can get the challenges by reconstructing the transcript and querying the random oracle. Since the random oracle is deterministic, the verifier should get the same challenges as the prover.
Evaluate vanishing polynomial . vanishing polynomial is public.
Evaluate Lagrange basis the Lagrange basis is also public.
Evaluate public input polynomial evaluation constructs the public input polynomial and evaluates it at .
The following steps are more interesting and involve batched KZG verification. We will show a high-level idea of how it works. The more formal explanation can be found in section 3.4 of the KZG paper.
Batched polynomial commitment scheme
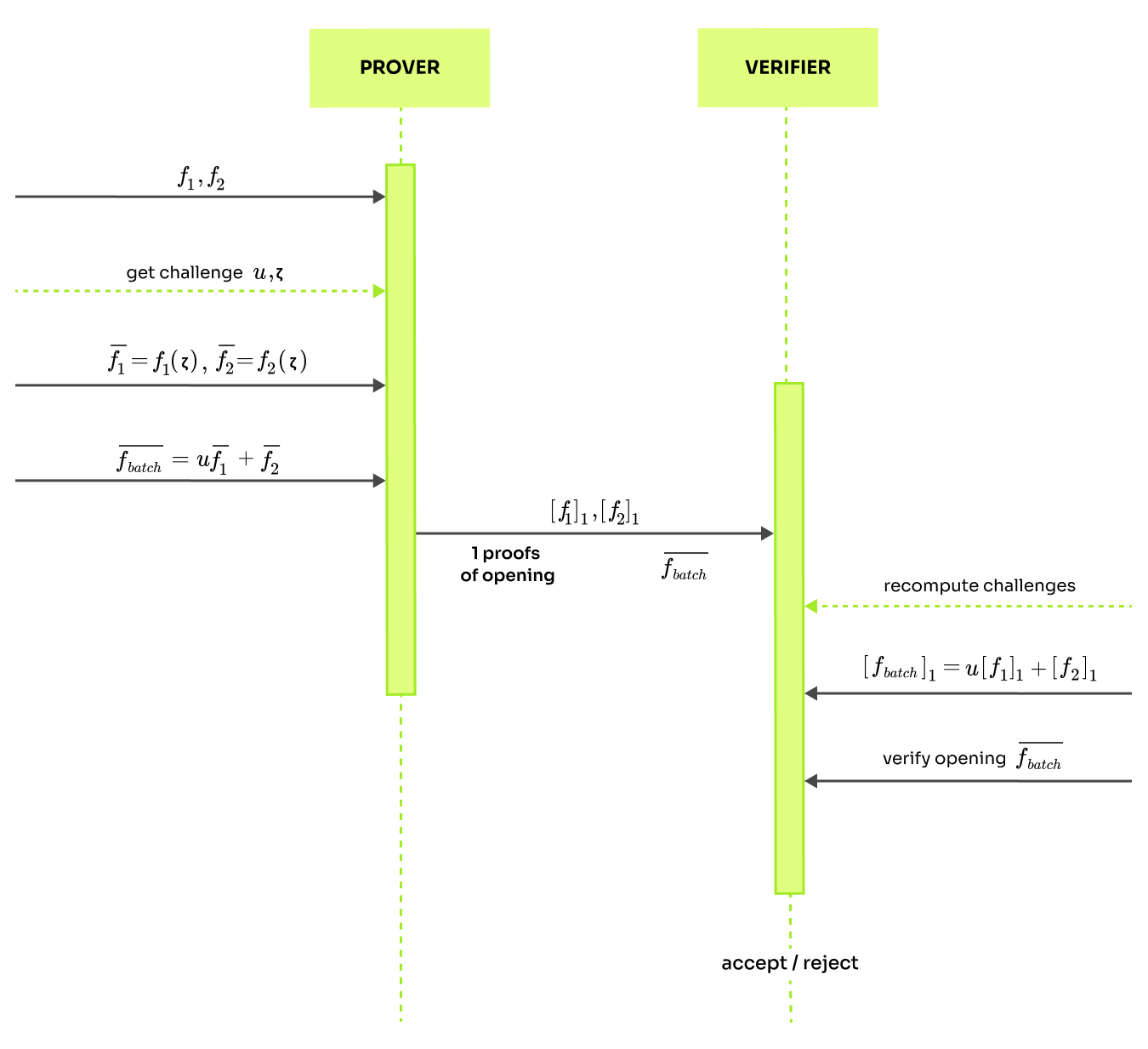
Say that the committer knows polynomials and wants to prove evaluations at randomly selected challenge . Rather than checking each claim independently, it is possible to batch them. We will perform a batched check using uniformly randomly selected as
Naturally, this approach is correct because if , then for any , the equality needs to hold. Moreover, the approach is also sufficiently sound. Notice that we can think about both and as linear functions with variable . If two linear functions are not identical, they have at most one crossing point, so the soundness error of the batching is at most , which is sufficiently low. So, with a very high probability, it holds that:
This means it is sufficient to verify the opening of the batched polynomial. Now, we will use a similar trick as in the linearization by defining . The commitment can be computed as . So the prover just needs to send commitments , opening and proof of the opening. Why is this better? The prover must only calculate one opening proof to the batched polynomial . If we performed this separately, there would need to be two opening proofs for .
Detailed explanation of the batched KZG can be found at blog by RisenCrypto, and a more general approach is described in the post PCS Mutli-proofs.
Batched Plonk verification
In the round 5 proofs of opening are consensed into and . They can be written in a simplified way as , and after some rearranging we get:
Now, we add a batch challenge to batch-equation as described in the previous section and sum the two equations together.
In steps 8-11 of the verification algorithm, the verifier calculates the commitments to . The final step checks the above identity using batched KZG-style verification with commitments and pairings:
This validates all the statements about the circuit described in the arithmetization. And that is all. Besides understanding the protocol, you hopefully also learned something about modern cryptography.
List of the PlonK blog posts:
- 1: Overview
- 2: Arithmetization
- 3: Math Preliminaries
- 4: KZG
- 5: Setup
- 6: Round 1
- 7: Round 2
- 8: Round 3
- 9: Round 4
- 10: Round 5
- 11: Verification
If you have any suggestions or improvements to this blog, send an e-mail to contact@maya-zk.com


